Your Guide to DevOps Secrets Management for SaaS
At its core, DevOps secrets management is all about getting a handle on every single password, API key, and digital certificate your team uses throughout the entire software lifecycle. It’s about securing them, controlling who can access them, and tracking their every use. For a growing B2B SaaS company, this isn't just a "nice-to-have" security measure; it's the foundation for preventing costly data breaches, nailing compliance, and freeing up your developers to build and ship code securely.
Why DevOps Secrets Management Is Critical for SaaS Growth

Think of your SaaS platform as a massive, sprawling headquarters. Every database, third-party service, and internal microservice is a securely locked room holding valuable assets. The keys to every one of those rooms are your secrets—passwords, API tokens, TLS certificates, and the like.
As your company grows, you're constantly adding more rooms and making more keys. New features, more integrations, and increasing automation mean you’re creating thousands of these digital keys. Without a central system to manage them, they end up scattered everywhere: hardcoded in source control, sitting in plain-text config files, or even shared in Slack channels and spreadsheets.
This is the digital equivalent of leaving your master keys under the doormat, taped to the window, and hidden in the mailbox. It's an accident waiting to happen, and it’s precisely why DevOps secrets management stops being a simple IT task and becomes a strategic business imperative.
From Technical Debt to a Strategic Asset
In the frantic early days of a startup, speed is everything. We’ve all seen it: a developer hardcodes an API key just to get a feature shipped, with a promise to "fix it later." That "later" rarely comes, and what you're left with is a mountain of security debt that only gets harder to pay down as the team and codebase expand.
A proper secrets management strategy flips this script, turning a dangerous liability into a powerful business asset. By putting a central system in place to manage these digital keys, you unlock several critical outcomes:
- Prevent Costly Data Breaches: You immediately eliminate the low-hanging fruit for attackers. A single exposed key can be the starting point for a catastrophic breach, and a central vault removes them from vulnerable locations like code repositories.
- Maintain Customer Trust: For B2B customers, security isn't a feature; it's a non-negotiable prerequisite. Showing you have a mature process for handling credentials is a powerful tool for winning and retaining business.
- Ensure Compliance: Frameworks like SOC 2, ISO 27001, and GDPR have stringent rules for credential management. A centralized secrets management system gives you the audit trails and access controls you need to pass those audits with confidence.
- Accelerate Secure Development: When developers have a clear, easy path to get the credentials they need, security stops being a roadblock. It becomes a seamless part of their workflow, allowing them to build faster and more securely.
The core idea is simple: make the secure way the easy way. A good secrets management system provides developers with on-demand, audited access to the credentials they need, exactly when they need them, without ever exposing the secret itself.
This urgency is clearly reflected in the market. The global secrets management market was valued at USD 4.22 billion in 2025 and is on track to hit USD 8.05 billion by 2030. This growth isn't surprising. As companies embrace automation and cloud-native tools, the number of secrets they have to manage explodes, making manual methods completely untenable. SaaS-based vault solutions are also making enterprise-grade security accessible to smaller teams, fueling a projected 15.5% CAGR through 2030. You can explore more on the secrets management market growth on Mordor Intelligence.
The Everyday Threats That Compromise SaaS Companies
When we talk about security threats, it’s easy to picture sophisticated, state-sponsored attacks. But for most growing SaaS companies, the real danger is much closer to home. It’s the small, everyday mistakes that create massive vulnerabilities.
Weak secrets management isn't a theoretical risk; it's a ticking clock. These aren't complex heists. They are common, preventable slip-ups that can lead to devastating downtime, lost customer trust, and damage to your brand that's hard to come back from.
Let's walk through a few of the most common threat scenarios that we see play out time and time again.
The Accidental Commit
It's a story that’s almost a cliché in engineering circles because it happens so often. A developer is under pressure to ship a new feature. To get a test working quickly, they hardcode a production API key directly into the source code. They finish their task, commit the changes, and push the branch to what they believe is a secure, private repository.
But "private" doesn't always mean safe. Within minutes, automated bots scanning platforms like GitHub can find the key. Before your team even has its morning coffee, an attacker could be siphoning off your customer data. The dangerous assumption is that private repos are secure, but research shows 8 times as many secrets are found in private repositories compared to public ones.
The Over-Privileged Microservice
Here’s another classic. You have a simple microservice that handles one job, like sending transactional emails. To function, it needs an API key for your email provider. The problem? The developer grabbed the master API key—the one with full administrative permissions to read, send, and delete anything.
Then, a vulnerability is discovered in an open-source library that the microservice depends on. An attacker exploits it, and suddenly that innocent little email service becomes a skeleton key to your entire communications platform. They can now access sensitive support tickets, impersonate executives, and create chaos. This is what happens when the principle of least privilege is just a talking point, not a practice.
The real danger isn't just one compromised service; it's the blast radius. An over-privileged secret turns a small security incident into a company-wide crisis, granting attackers far more access than they should ever have.
The Lingering Ghost
An engineer leaves your company on great terms to start a new role. Everyone wishes them well, but in the rush of transitioning projects, nobody revokes their personal access key to your cloud infrastructure. It’s a simple oversight.
Weeks or months later, that former employee's laptop is stolen, or their credentials are leaked in a completely unrelated data breach. Now, an attacker has a valid, trusted key that lets them walk right through your front door. They can spin up costly crypto-mining rigs on your account, steal data, or deploy ransomware. In fast-moving teams, incomplete offboarding checklists leave these dangerous backdoors open indefinitely.
The Eavesdropper
Many teams still share secrets in plain text, thinking it's fine "just this once." A database password gets sent over Slack, an API token is pasted into a Jira ticket, or a TLS certificate is attached to an email. According to the 2025 Verizon Data Breach Investigations Report, stolen credentials were the initial entry point in 22% of breaches.
Every one of these messages is a target. A compromised Slack account or a flaw in a third-party project management tool is all an "eavesdropper" needs. They can quietly collect a treasure trove of your company's most sensitive credentials, giving them everything they need to orchestrate a much larger attack.
4 Core Secrets Management Patterns You Need to Know
To get a real handle on DevOps secrets management, you have to understand the common playbooks, or "patterns," that teams use. These strategies run the gamut from dangerously simple to impressively automated, and knowing the difference is what will set your growing SaaS company up for success.
The story almost always starts with quick-and-dirty methods born out of convenience. Unfortunately, those shortcuts quickly turn into massive liabilities as soon as you start to scale.
The Antipatterns: Hardcoding and Basic Environment Variables
Let's start with what not to do. The most basic—and by far the riskiest—method is hardcoding secrets. This is when a developer puts an API key, password, or auth token directly into the source code. It usually happens with good intentions, like trying to get a new feature working quickly with the plan to "fix it later."
Of course, "later" often never comes. Those temporary secrets get forgotten, committed to a Git repository, and suddenly they’re exposed to anyone with access to the codebase.
A small step up from that is using basic environment variables. Instead of being baked into the code, the secret lives on the server or container running the app. While it does get the credential out of your source code, it just kicks the can down the road. The secrets are usually stored in plain text, making them visible to anyone who can get onto that machine. Worse, they can easily leak into logs or debugging outputs.
Both of these methods completely fall apart at scale. They offer zero central control, no audit trail, and make rotating credentials a painful, manual process. This is how small oversights snowball into major security incidents.
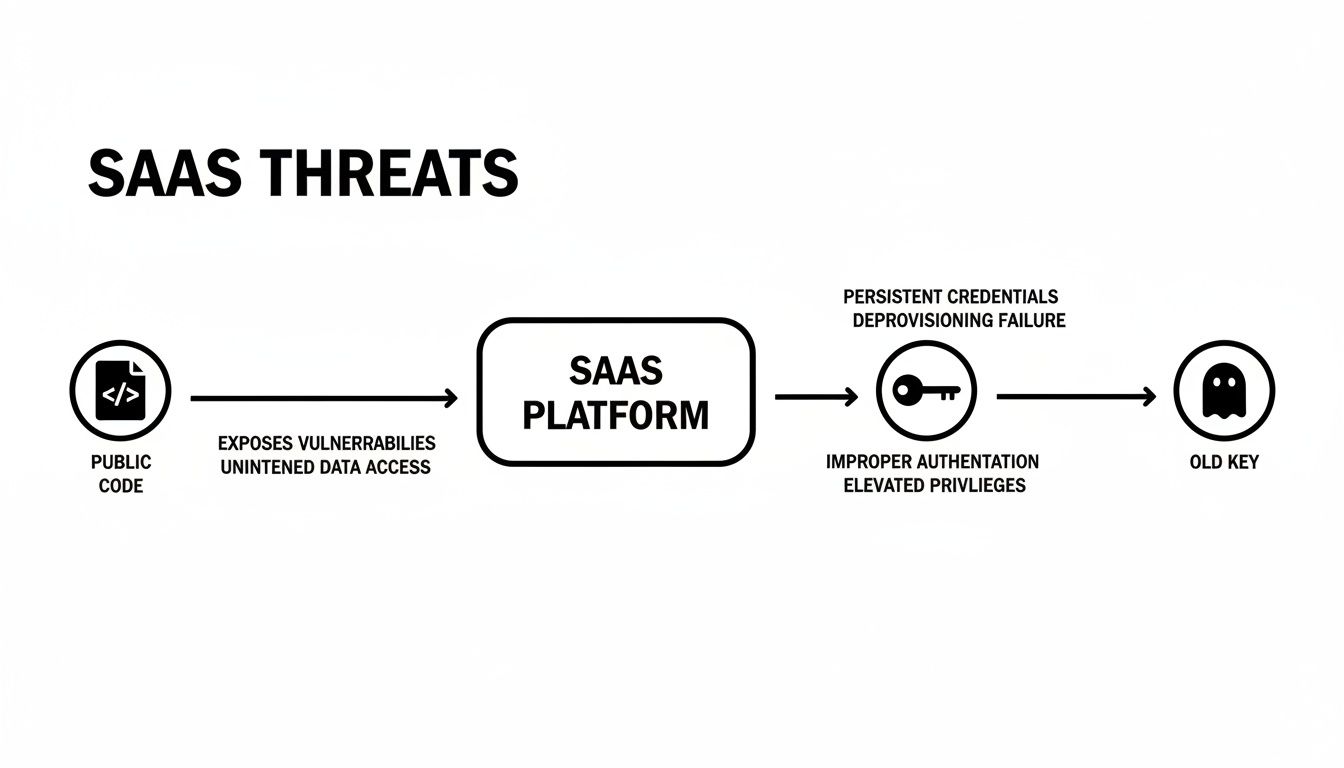
As you can see, leaving old keys lying around or publishing code with credentials stuck inside creates a direct path for attackers to compromise your entire platform. To build a truly secure system, we have to move past these fragile methods and adopt patterns built around a strong, centralized core.
The Digital Vault: Your Security Foundation
The first real step up the maturity ladder is adopting the digital vault pattern. Think of it as a high-security bank vault for all your digital credentials. Tools like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault serve as a single, encrypted place to store everything.
Instead of secrets being scattered all over your infrastructure, they live in one spot with airtight access controls. Applications and developers don't grab secrets directly anymore. Instead, they have to prove their identity to the vault, which then grants them the specific credential they need based on their permissions.
A digital vault transforms secrets management from a chaotic free-for-all into a controlled, auditable process. It's the foundational building block for all modern security patterns, giving you a single source of truth for every credential.
This central control is a game-changer. But the real power of a vault is that it unlocks even more dynamic and secure ways of handling secrets.
To help you decide which approach fits your team, here’s a quick comparison of the patterns we've discussed so far, plus the more advanced ones we'll cover next.
Secrets Management Patterns At a Glance
This table offers a practical comparison of secrets management methods, evaluated by security level, scalability, and operational complexity for modern SaaS teams.
| Pattern | Security Level | Scalability | Best For |
|---|---|---|---|
| Hardcoding | Very Low | None | Quick local tests only; never in production. |
| Environment Variables | Low | Low | Simple, non-critical apps where rotation is infrequent. |
| Digital Vault | High | High | Any team needing centralized control, auditing, and a foundation for automation. |
| Ephemeral Credentials | Very High | High | Securing automated access to databases, cloud services, and internal APIs. |
| Secret Injection | Very High | High | Containerized environments (like Kubernetes) and serverless functions. |
As you can see, moving toward vaults and dynamic patterns dramatically improves both security and your ability to scale.
Ephemeral Credentials: The Self-Destructing Message
Once you have a vault in place, you can start using ephemeral credentials, also known as dynamic secrets. This is where things get really cool. Instead of giving an application a permanent password that could be stolen and reused, the vault generates a unique, temporary credential that’s only valid for a few minutes or even seconds.
It's like giving a courier a key that dissolves after one use. An application requests access to a database, the vault generates a one-time username and password, and as soon as the task is done, that credential expires and becomes useless. This shrinks the window of opportunity for an attacker from months or years down to almost zero. Even if a temporary secret is somehow compromised, it’s worthless because it expires almost immediately.
Secret Injection: The Secure Delivery System
Finally, secret injection automates the "last mile" of the process: getting the secret securely to the application that needs it. With this pattern, the application doesn't have to pull the secret from the vault itself. Instead, a trusted process "injects" the secret directly into the application's running environment just in time.
A classic example is in a Kubernetes environment. A "sidecar" container can run alongside your main application. This sidecar's only job is to authenticate with the vault, retrieve the secret, and write it to a shared memory volume that only the application container can read. The application gets the credential it needs at the exact moment it's needed, without ever storing it on a disk or even knowing where it came from. This is a core principle for building a robust system that fully embraces DevOps and continuous delivery.
By combining a central vault with dynamic patterns like ephemeral credentials and secret injection, you create a system where secrets are tightly controlled, automatically managed, and delivered on a need-to-know basis. This takes the security burden off your developers and makes the most secure path the easiest one to follow.
Essential Best Practices for Bulletproof Security

Moving away from scattered, ad-hoc credential handling isn't just about installing a new tool—it's about fundamentally changing how your team thinks about security. By embracing a few core best practices, you can shift from a reactive, fire-fighting mode to a proactive stance that builds a rock-solid foundation for growth.
Think of these practices as the non-negotiable ground rules for your entire DevOps secrets management strategy. They represent the difference between just having a vault and actually getting real security value out of it.
Enforce the Principle of Least Privilege
The Principle of Least Privilege (PoLP) is the absolute bedrock of modern security. The idea is simple but incredibly effective: any user, application, or service should only have the bare-minimum permissions needed to do its job. And nothing more.
It’s like giving a plumber a key that only opens the one mechanical room they need to access, not a master key to the entire office building. If that specific key gets lost, the potential damage is completely contained. This is exactly how PoLP works in your infrastructure, dramatically shrinking the "blast radius" if a component is ever compromised.
For instance, a reporting service doesn't need full read/write access to your main database. Instead, give it read-only permissions for the exact tables it queries. That one small change prevents a breach of the reporting service from becoming a catastrophic data loss event.
Automate Secret Rotation Systematically
Even when stored in a secure vault, static, long-lived secrets are a ticking time bomb. An API key or password that never changes is a permanent target for attackers. Automated secret rotation defuses this threat by programmatically changing credentials on a set schedule, all without a human ever touching them.
This is a game-changer for a few key reasons:
- Limits Exposure Time: If a secret does get compromised, it's only valid until the next rotation. This shrinks an attacker's window of opportunity from months or years down to just hours or days.
- Invalidates Leaked Credentials: It automatically cleans up your security posture by rendering old, forgotten, or potentially exposed secrets totally useless.
- Reduces Manual Work: It frees up your engineers from the mind-numbing and error-prone task of manually updating passwords across dozens of systems.
A good secrets management platform can connect to a database, create a new password, update the database user, and save the new secret back to the vault—all in one seamless, automated workflow.
Implement Comprehensive Auditing and Monitoring
If your vault is a fortress, then your audit log is the 24/7 surveillance system watching every door and window. It's absolutely critical to have an immutable record of who (or what) accessed which secret, and when. This isn’t just for passing a compliance audit; it's your primary tool for incident response.
A detailed audit log helps you answer the most important questions after a security incident: How did the attacker get in? What did they access? How far did they get? Without it, you're flying blind.
Robust auditing helps you spot anomalies that could signal a breach, like a service suddenly asking for a secret it never uses or a developer accessing production keys at 3 AM. This kind of visibility is essential for catching threats early. For more on this, check out these secrets management best practices for Secure DevOps.
Integrate Security into Your CI/CD Pipeline
Finally, security shouldn't be a roadblock that developers have to work around. It should be a set of guardrails that keeps development moving forward safely. Integrating secrets management directly into your Continuous Integration/Continuous Deployment (CI/CD) pipeline weaves security into the fabric of your workflow.
This approach, often called DevSecOps, has real financial upside. Organizations with deeply integrated DevSecOps practices report 15% lower security remediation costs. What's more, high-performing teams are 3.3 times more likely to build security into the design phase, with 74% of companies calling it a top priority.
Instead of developers manually handling credentials, the pipeline does it for them. A build job can fetch a temporary token from the vault to run integration tests, and a deployment script can inject the final production secrets into an application's environment moments before it starts. This automation not only tightens security but also makes your developers faster.
This is a key part of mastering your software supply chain, which is often automated with tools like Ansible. To learn more about that, check out our guide on Ansible best practices.
Your Step-By-Step Implementation Roadmap
Tackling DevOps secrets management can feel like a massive project, but it doesn't have to be a painful, all-at-once overhaul that grinds your development to a halt. The smart approach is to treat it as a journey you take in clear, manageable steps.
This roadmap is built specifically for growing SaaS teams. It’s all about making steady progress and getting the biggest security wins first, creating a solid foundation you can automate and build on later.
Step 1: Discover and Triage
You can’t secure what you don't know exists. The first, and most important, step is to find every single secret scattered across your environment. Think of it less like a manual treasure hunt and more like a systematic sweep with automated tools.
These scanners will dig through your:
- Code Repositories: Combing through every branch and commit history in places like GitHub or GitLab for hardcoded API keys, passwords, and tokens.
- Configuration Files: Finding credentials accidentally left exposed in YAML, JSON, or
.envfiles. - CI/CD Pipelines: Inspecting build logs and pipeline configurations where secrets often appear in plain text.
- Collaboration Tools: Checking for credentials shared in plaintext within Slack, Jira, or Confluence.
Once the scan is done, you need to triage the results. Not every exposed secret is a five-alarm fire. Prioritize them based on the environment (production keys are always top of the list) and the level of access they provide. This gives you a risk-based backlog so you know exactly where to start.
Step 2: Choose Your Central Vault
With a clear map of your secret sprawl, it's time to establish a single source of truth: your central vault. This digital fortress is the heart of your entire secrets management strategy. The right one for you will depend on your tech stack, team skills, and budget.
Here are the main contenders:
- Cloud-Native Solutions: If you're all-in on a single cloud, using AWS Secrets Manager, Azure Key Vault, or Google Cloud Secret Manager is usually the path of least resistance. They integrate seamlessly with their own services and are pretty straightforward to set up.
- Cloud-Agnostic Tools: For teams running in multi-cloud or hybrid environments, a platform like HashiCorp Vault offers a consistent approach everywhere. It’s more involved to manage but gives you incredible flexibility and power, so you're not locked into one vendor.
- Developer-Focused Platforms: Tools like Doppler or Infisical are designed with the developer experience in mind. They're great for teams that want to adopt secure practices quickly without a steep learning curve.
The goal is to pick a tool that works for your team right now but can also grow with you. Starting with your cloud provider’s native solution is often a pragmatic first move to get quick wins on the board.
Step 3: Pilot and Migrate
Whatever you do, don't try to boil the ocean. A "big bang" migration of all your secrets at once is a recipe for broken builds and late-night panic. Instead, start small with a pilot project.
Pick a single, low-risk application—a new service you're building or even an internal tool is a perfect candidate. Use this pilot to walk through the entire process: get the secrets into your new vault, update the app to pull them securely, and bake it all into your deployment workflow.
This pilot project is your sandbox. It gives your team a low-pressure environment to learn the tool, document the steps, and smooth out any wrinkles before you touch a critical production system. Once you've nailed it for one application, you have a blueprint to repeat for everything else.
Step 4: Automate and Enforce
With a vault in place and a proven migration process, the final step is to make security the default—the easiest path for every developer. You do this by weaving secrets management directly into your automated workflows.
Connect your vault to your CI/CD pipeline. This lets your build and deployment scripts automatically inject secrets where they need to go at runtime, meaning developers never have to see or handle them. Managing credentials becomes just another automated part of the DevOps life cycle, not a manual chore.
Finally, enforce the new rules. Use pre-commit hooks to block any code with new hardcoded secrets from ever making it into your repository. Set up automated rotation for database passwords and API keys. When the secure way is the only way, you build a resilient system that scales right along with your business.
Alright, you've got the tools and a plan. But before you dive into implementing DevOps secrets management, let's talk about the roadblocks that trip up even seasoned teams. Knowing what to watch for is half the battle, and learning from others' battle scars is the fastest way to build a system that's genuinely secure and resilient.
Even with the best intentions, things can go wrong. Let’s walk through the most common traps I’ve seen teams fall into.
The Brittle Vault Problem
So you’ve done it. You’ve corralled all your credentials into a shiny new centralized vault. Big win, right? Well, maybe. But what happens if that vault goes down?
If your entire infrastructure needs the vault to start up, an outage means everything—and I mean everything—grinds to a halt. Your apps can't fetch database passwords. Your microservices can't get their API keys. Your whole platform is offline. It’s a classic case of creating a new single point of failure, and it's a critical mistake for any SaaS company where uptime is king.
You have to treat your secrets vault like any other piece of mission-critical infrastructure. To sidestep this disaster, you absolutely must:
- Design for High Availability (HA): Run your vault in a cluster spread across multiple availability zones or even regions. If one node goes dark, the others are ready to pick up the slack without a blip.
- Have a Real Disaster Recovery Plan: This isn't just about backups; it's about having a tested recovery plan. Set up regular, automated backups and practice restoring them. Don't wait for a real outage to find out your backup process is broken.
- Use Caching (Carefully): Some tools let applications securely cache secrets for a short time. This can be a lifesaver, allowing an app to weather a brief network hiccup or vault restart.
A vault that isn't highly available can easily become a bigger operational risk than the secret sprawl it was meant to solve. Your security solution should never be your single biggest point of failure.
The Overly Permissive Vault
Another trap I see all the time is treating the vault like a glorified password file. Teams get all their secrets moved over but then fail to lock down the permissions inside. They end up giving developers or services sweeping access to everything.
This completely misses the point.
Imagine a scenario where a developer working on a staging environment can also pull production database credentials. You've just recreated the risk of a shared spreadsheet, but in a much more expensive tool. The principle of least privilege isn't just about who can access the vault; it's about what they can access within it.
Secret Sprawl 2.0
You've launched your vault, migrated every known secret, and declared victory over sprawl. But a few months down the line, you find new secrets creeping back into the codebase. A developer on a tight deadline hardcoded an API key for a "quick fix," or someone else stashed a password in an environment variable again.
This is what I call "Secret Sprawl 2.0." It happens when security isn’t fully baked into the daily workflow. A vault isn't a one-and-done cleanup project; it demands ongoing vigilance.
To stop the sprawl from returning, you need a few things in place:
- Continuous Scanning: Keep running secret detection tools across your repositories and CI/CD pipelines. You need to catch new secrets the moment they appear.
- Pre-Commit Hooks: This is your first line of defense. Implement hooks that automatically block any commit containing something that looks like a secret.
- Make the Secure Way the Easy Way: This is the most important part. If getting a secret from the vault is a pain, developers will find a way around it. Your job is to provide simple CLIs, clear documentation, and easy-to-use SDKs.
By getting ahead of these common pitfalls—the single point of failure, lazy permissions, and the inevitable return of sprawl—you'll be on your way to building a secrets management system that’s truly effective, not just another tool.
Frequently Asked Questions About Secrets Management
As you start mapping out your DevOps secrets management strategy, the real-world questions always start to bubble up. Let's tackle some of the most common, in-the-weeds concerns we see from founders and tech leads.
What's the Difference Between a Secret Manager and a Password Manager?
It’s a great question, and the answer comes down to who—or what—is using it.
Think of a password manager like 1Password or LastPass as something built for people. Its job is to help an individual securely store their personal logins and fill them into websites and apps.
A secrets manager, on the other hand, is built for machines. It's designed specifically for your applications, services, and infrastructure to programmatically—and securely—request things like API keys, database credentials, or TLS certificates. They come with critical features like robust APIs, detailed audit logs, and the ability to create temporary secrets on the fly, none of which a personal password manager needs.
Can We Just Use Our Cloud Provider's Built-in Tool?
Yes, you absolutely can. For many teams just getting started, using a service like AWS Secrets Manager, Azure Key Vault, or Google Cloud Secret Manager is the perfect first step. It’s often the path of least resistance.
These tools are woven directly into their cloud ecosystems, so getting them up and running is usually straightforward. The main catch, and it's a big one, is the potential for vendor lock-in. If your company already operates across multiple clouds or has a hybrid setup, relying on a single provider's tool can get complicated. In those cases, a cloud-agnostic platform like HashiCorp Vault might be a better long-term play, giving you one source of truth for secrets everywhere.
How Do We Secure Secrets in a Legacy Application?
This is a classic—and very real—headache. It's rarely practical to completely rewrite an older, monolithic application just to have it pull secrets from a modern vault. Thankfully, there's a clever workaround: the "sidecar" pattern.
A sidecar is a tiny, separate container that runs right alongside your main application. Its only job is to talk to the vault, grab the secret your app needs, and then pass it to the app through a simple local file or environment variable.
This approach is brilliant because it lets you bolt on modern secrets management without ever having to touch the legacy application's core code.
Where Should the Very First Secret Be Stored?
Ah, the "chicken-and-egg" problem of secrets management. Your application needs a secret to access the vault, but where do you safely store that first secret?
The modern best practice is to stop thinking about storing that first secret at all. Instead, you use the cloud platform's own Identity and Access Management (IAM) system. You grant the machine itself—whether it's an EC2 instance, a container, or a Kubernetes service account—a specific IAM role. That role gives it the inherent permission to authenticate with the vault and request other secrets. This completely sidesteps the need to ever store a long-lived credential on the machine in the first place.
At MakeAutomation, we specialize in implementing the automation and security frameworks that help SaaS companies scale without compromising on security. If you're ready to move beyond manual processes and build a resilient, automated foundation for your business, we're here to help. Explore our automation solutions and book a consultation today.







